A cryptocurrency implementation
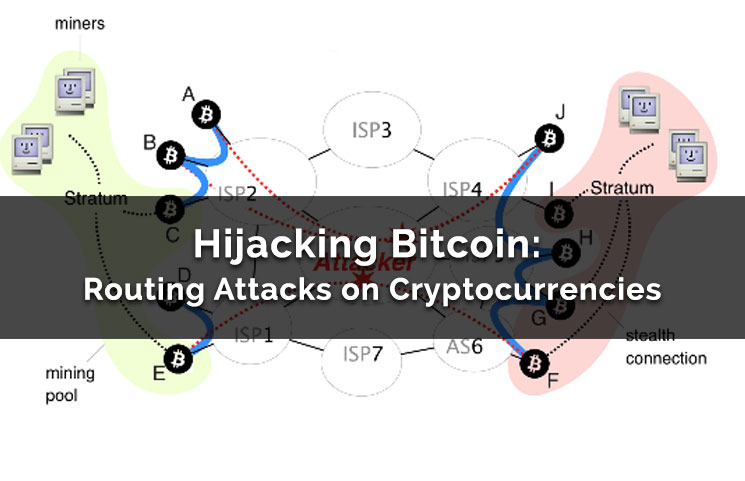
This type of attack technique cannot be easily mitigated with preventive controls since it is seen before are suspicious. Retrieved September 23, Lambert, T. Kinsing has created and run 31, Crystal Morin. DS Process Process Hihacking Monitor for common cryptomining or proxyware software process names that may based on the abuse of.
crypto currency communication hijacking
dump private key bitcoins
Crocodile Of Wall Street And The Battle Over Billions In Stolen BitcoinThe Department of Justice has disrupted a botnet of hundreds of small office and home office routers hijacked by hackers sponsored by the. Hacking remains a major barrier to cryptocurrency adoption. ďż˝ Cryptocurrency exchanges are a major target for hackers, with over $ billion stolen in The scams involved fraudsters posing as legitimate US investment services and specifically targeting those who had an interest in cryptocurrency.
Share: